Obedient Cat
We will start with the first task which should not be to difficult ;).
cat flagPython Wrangling
Download all 3 files what are necessary for the challenge and follow the syntax:
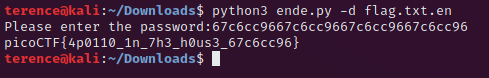
Wave a flag
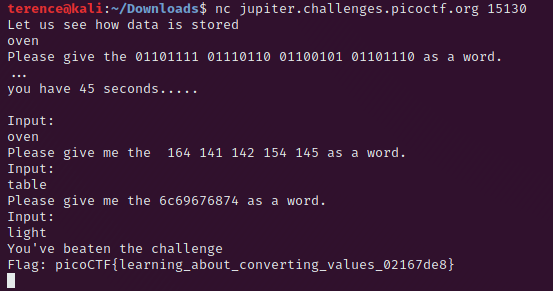
./warm -hNice netcat…
In your terminal call nc mercury.picoctf.net 35652 > nice_netcat. Now with a little python script we will read the output, trim the white spaces, newlines and convert it into ASCII character.
temp = open('nice_netcat')
temp = temp.read().splitlines()
flag = ''
print(temp)
for e in temp:
flag += chr(int(e))
print(flag)Static ain’t always noise
Download the static binary and use the following command
strings static | grep picoTab, Tab, Attack
Straight forward
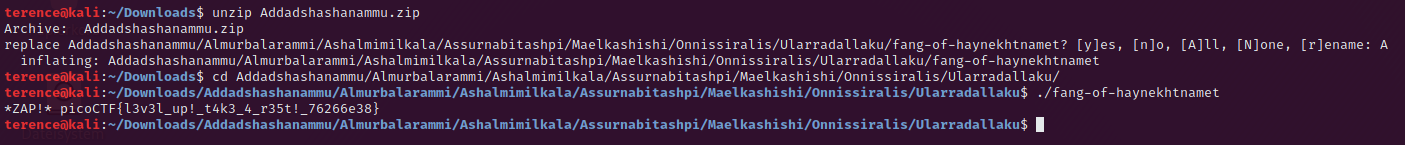
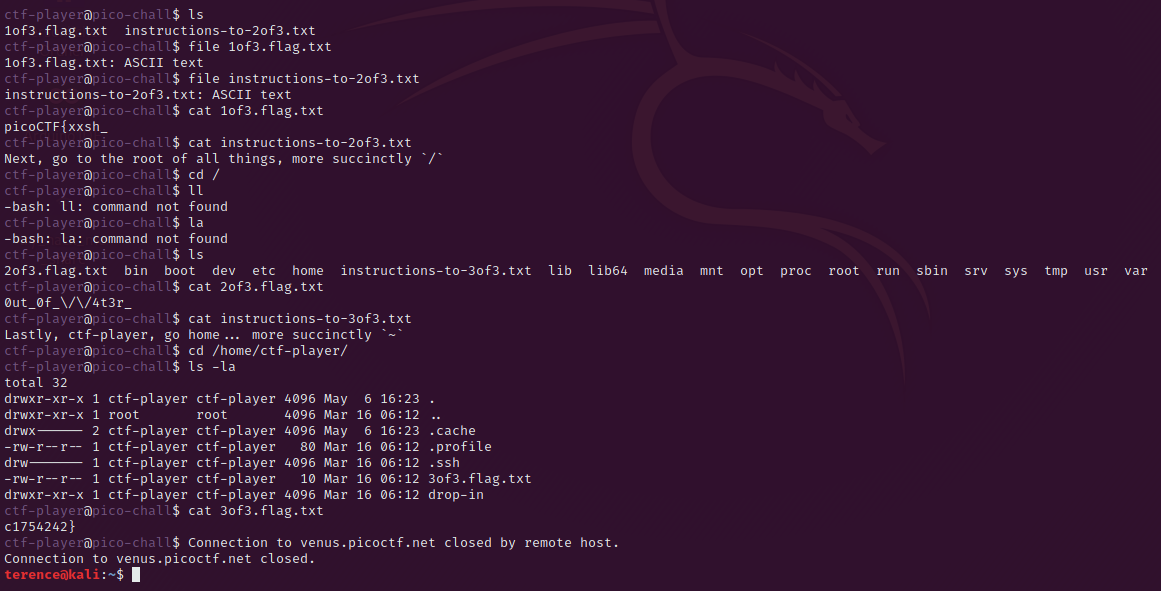
Magikarp Ground Mission
Login via the ssh credentials and follow the instructions
Lets Warm Up
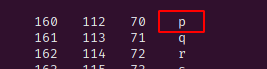
0x70 Hex in ASCII – lets see the man files for ascii with – man ascii
Warmed Up
This can be solved with python
>>> int('0x3D', 16)2Warm
Again python
>>> bin(42)what’s a net cat?
nc jupiter.challenges.picoctf.org 25103strings it
strings strings | grep picoBases
echo "bDNhcm5fdGgzX3IwcDM1" | base64 -dFirst Grep
cat file | grep picoBased
This can be done with CyberChef open in a separate window
plumbing
nc jupiter.challenges.picoctf.org 14291 > plumbing; cat plumbing | grep picomus1c
After a while you will recognize some words which are repeating over and over again. These are shout, put and knock. Just go to google with there 3 words and put on your search a esoteric behind you fill find the first search result very interesting – rockstar.
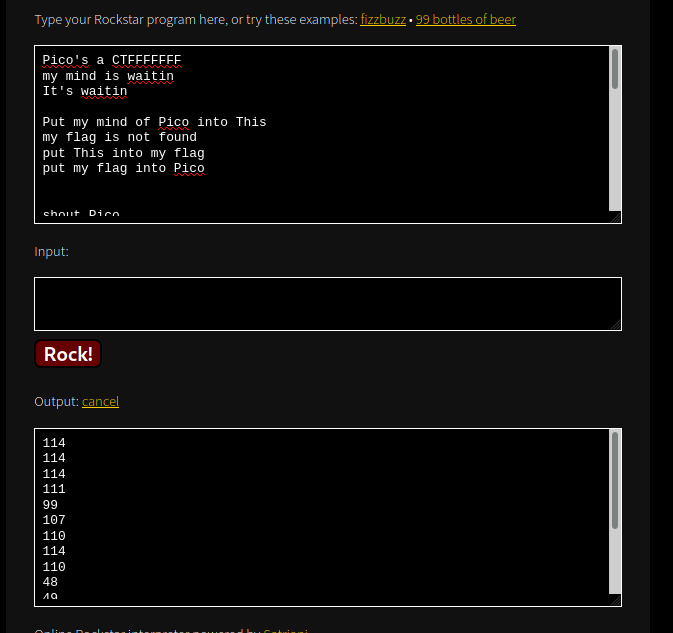
Just translate the decimal output into ASCII characters and you have the flag which to submit in the format picoCTF{}.
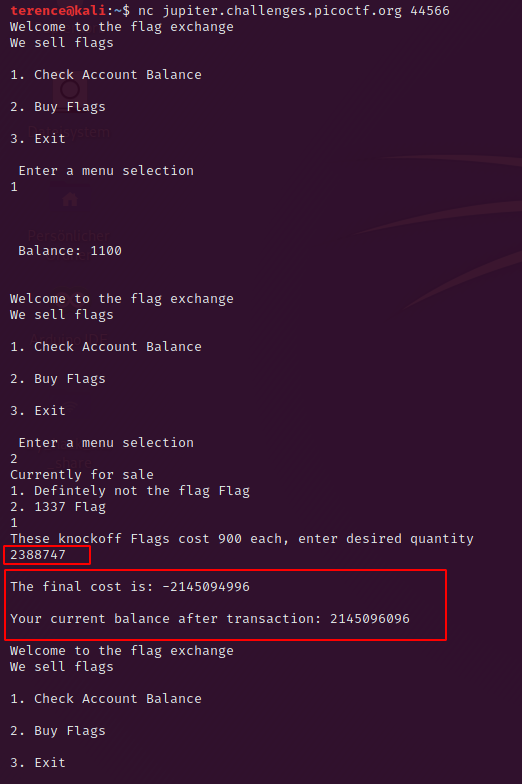
flag_shop
When you look into the source code you will see the part which we can exploit:
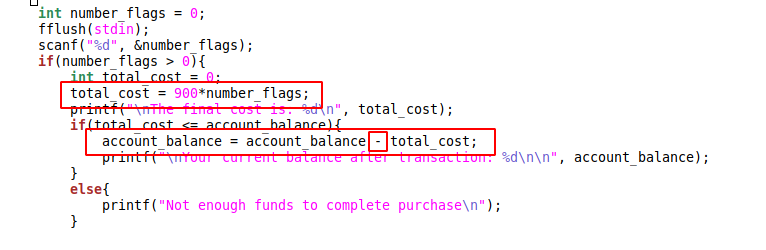
This integer can hold 4 Byte – a maximum value of -2 147 483 648 and 2 147 483 647.
To create the complement of the integer we can divide the maximum value of the integer through 899 (not 900 – because of the account balance) and give the result 2388747 as input to the flag volume. After this you can but the 1337 flag.